‘True Life Crime: The $5 Million Phone Hack’ on Paramount+ features the incredible story of Joel Ortiz, a young hacker from Boston, Massachusetts, who stole millions in cryptocurrency through multiple online fraudulent schemes. The episode traces his humble roots, and how he skyrocketed into the hacking community with his dedication and merit before settling on stealing money.
Who Is Joel Ortiz?
Joel Ortiz grew up in Boston, Massachusetts, and his mother was an immigrant from Puerto Rico with a 100% disability due to a back injury. With no father in the picture, he grew up in poverty and alone, except for his Internet friends. He was a tech-savvy kid, learning to cheat and exploit video games in early 2011, and was just shy of 13 when he started advertising Call of Duty cheat lobbies he had set up and charged people for accessing them. Over the next six years, his online videos traced him falling deeper into the online CD communities.

Taking a peek at his early videos, he posted more about modding, bugging, and hacking into the games he played until late 2013. While his initial online behavior was similar to many of his contemporaries, multiple videos uploaded on his channel showed he favored a forum called NextGenUpdate. Now closed for several years, the online outlet hosted one of the largest communities for sharing console gaming cheats, exploits, and bugs. However, much of video game cheating is linked to actual with actual hacking communities.
The episode showed some archived screenshots of the website where people had posted about remote administration tools, SQL injection, account cracking, phishing, and encrypting malware — the foundations for getting involved in online fraud. While an introverted Joel had a negligent social life as a high schooler, he had an explosive online presence, with 4,051 posts and becoming a moderator on NextGenUpdate. By then, he had begun idolizing hackers like George Hotz — who had been sued by Sony for reverse engineering the PlayStation 3.
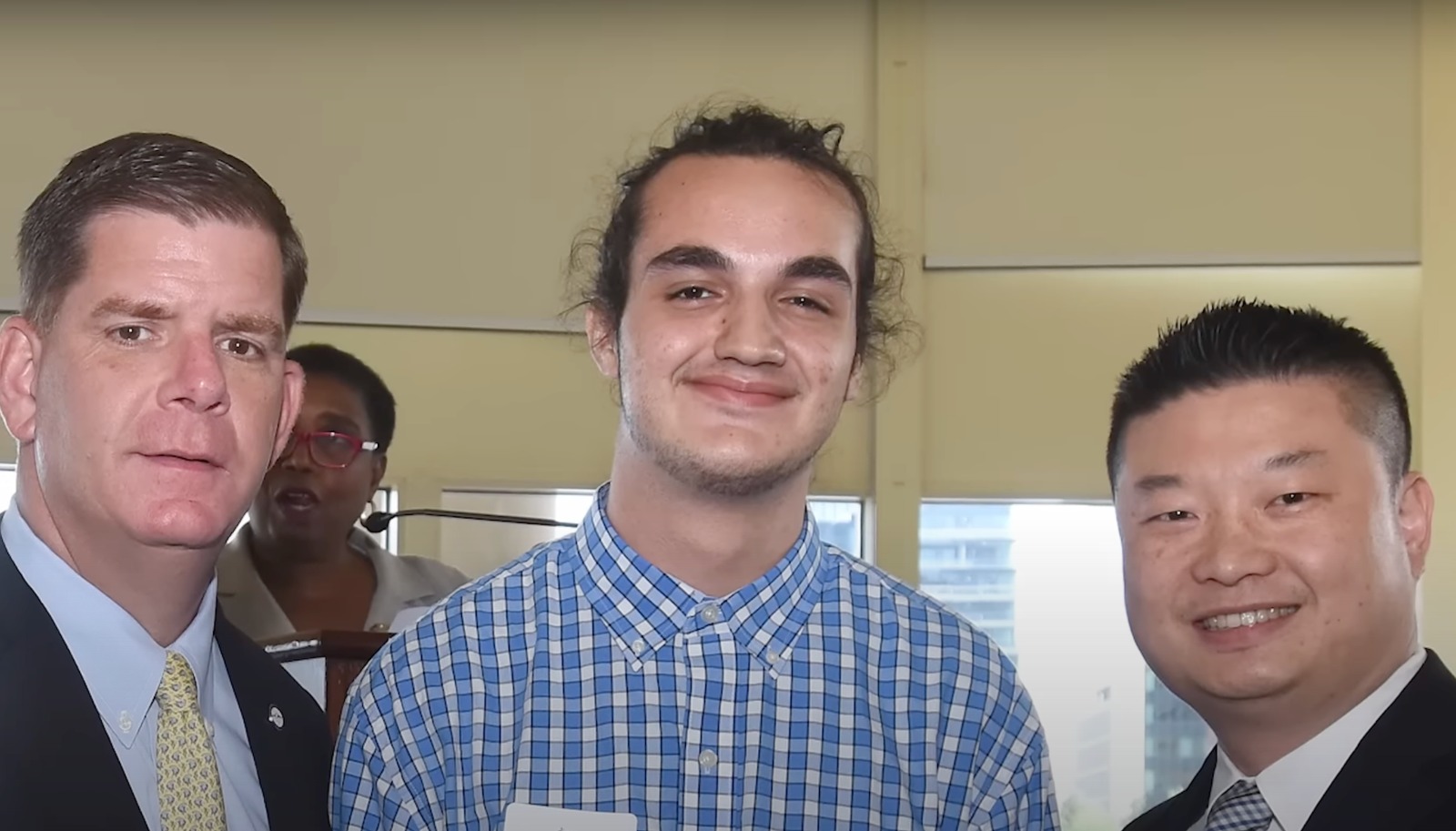
By 2016, Joel was in the last year of high school, excelling academically, leading the robotics team, and teaching other kids programming. Meanwhile, he had been teaching himself how to code and often bragged on social media about bypassing the security of certain websites and accumulating user information. In June 2016, he awaited to hear from The University of Massachusetts Boston, where he had applied to study computer science. In the meantime, he decided to make money by being involved in online theft.

According to the show, Joel learned how to steal valuable social media accounts and possessed a collection of one-letter Twitter and Instagram accounts. These are exceedingly rare, as they would have had to be created when these platforms were initially launched. As such handles were means of bragging rights online, they were expensive, and Joel became a member of OGUSERS, a website where users traded such invaluable account handles. For the first time, he began making money and got a taste of the fine things in life.
However, driven by his childhood financial insecurity, Joel was driven to make more money by hacking into the more coveted Instagram handles that were not easy to get a hold of. As the world around him was changing, he devised newer and more efficient hacking methods for social media accounts. Cryptocurrency, like Bitcoin, was grabbing the headlines, setting in a new dawn of online thefts and fraud. Joel and his online hacking compatriots soon switched their novel ideas for stealing Instagram accounts to a more sinister crime called SIM swapping.
Joel Ortiz is Serving His Sentence Today
In SIM swapping, hackers manipulate mobile phone carriers to transfer access from a targeted person’s registered SIM card to one of their own. While some cases might involve internal sabotage, most digital intruders gain access by answering security questions gleaned from a person’s social media profile or through phishing emails and Facebook chain posts. Exerting control over text messages allows them to circumvent most digital security measures on banking, social media, and cryptocurrency accounts.
In one attack, Joel targeted a cryptocurrency entrepreneur and stole $1.5 million. The victim stated, “I looked at my phone, and it was dead.” REACT investigators began tracking Joel’s activities in February 2018 when a Santa Clara County resident suspected he was a victim of such a scheme. Upon investigation, they discovered the victim had lost $10,000 worth of Bitcoin. In a matter of days, the presumed hacker even contacted the victim’s wife and sent text messages to his daughter, including the text, “TELL YOUR DAD TO GIVE US BITCOIN.”
Investigators executed a warrant against AT&T, revealing that the victim’s number had been associated with two Samsung devices on the day of the hack — devices the victim did not possess. Using the IMEI numbers to identify these phones, a subsequent warrant was issued to Google for data associated with them. This search uncovered several email accounts, one of which contained a photo of Ortiz displaying his Massachusetts ID, linking him to the account. They also found several suspicious and criminally related activities by the young hacker.
Police sources found Joel had uploaded YouTube tutorials on exploiting social media and phone company websites and his purchase of the domain www.tw-tter.com, suspected for use in phishing attacks. This discovery ultimately revealed at least $1.5 million in illicit activity. The investigators issued another warrant to AT&T to find “any and all accounts” linked to his phone and found 40 possible victims. A further warrant on the cryptocurrency exchanges he used revealed he moved over $1 million worth of various cryptocurrencies.

Joel showcased a lavish lifestyle online, likely financed by stolen funds. He was apprehended at Los Angeles International Airport on July 12, 2018. Following his arrest, the REACT task force apprehended other significant SIM swap suspects, including Xzavyer Narvaez, who was 19 in August 2018. His involvement was apparently revealed through emails found on one of Joel’s phones. Joel was initially charged with 41 counts, including multiple charges of identity theft, hacking, and grand larceny, and linked to 13 identified victims.
The authorities have managed to recover only about $400,000 of the millions he is believed to have stolen. He pled no contest in January 2019 to eight counts of identity theft and computer crimes and was sentenced to a decade in what was believed to be the country’s first-ever arrest and conviction for SIM swapping. As part of his plea deal, he agreed to pay restitution to the eight who suffered some monetary loss. He, 25, is serving his sentence at FCI Allenwood Medium and is slated to be released in April 2028.
Read More: Laurence Austin Murder: Where Are James Van Sickle and Christian Rodriguez Now?


You must be logged in to post a comment.