When Daniel Rigmaiden was apprehended for wire fraud, identity theft, mail fraud, and unauthorized computer access back in 2008, no one could’ve expected his case to unfold the way it did. After all, as explored in ‘Web of Make Believe: The Stingray,’ while it’s undeniable that he did commit extensive financial crimes, the key tool the officials used to locate him is questionable at best. So now, if you wish to learn precisely what a Stingray device is, how it affects our overall individual privacy, and which agencies have open access to it, we’ve got the essential details for you.
What is Stingray?
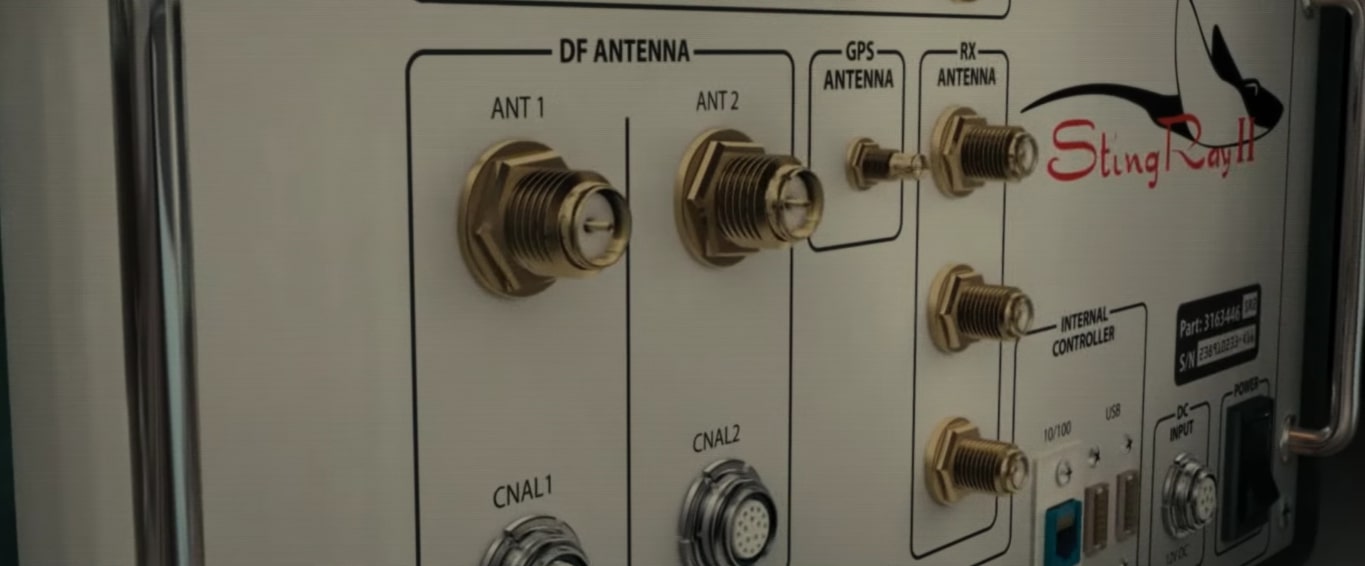
A Stingray is a general, commercial term for a somewhat still secretive law enforcement surveillance technology known as an International Mobile Subscriber Identity-catcher (or an IMSI-catcher). It is essentially a cell-site simulator that forces every nearby wireless communication device into connecting to it rather than an actual tower to reveal their exact individual IMSI number. From there, gathering not just the devices’ locations (almost to a tee) but also intercepting mobile phone traffic and recording calls, numbers, as well as text messages becomes entirely too possible.
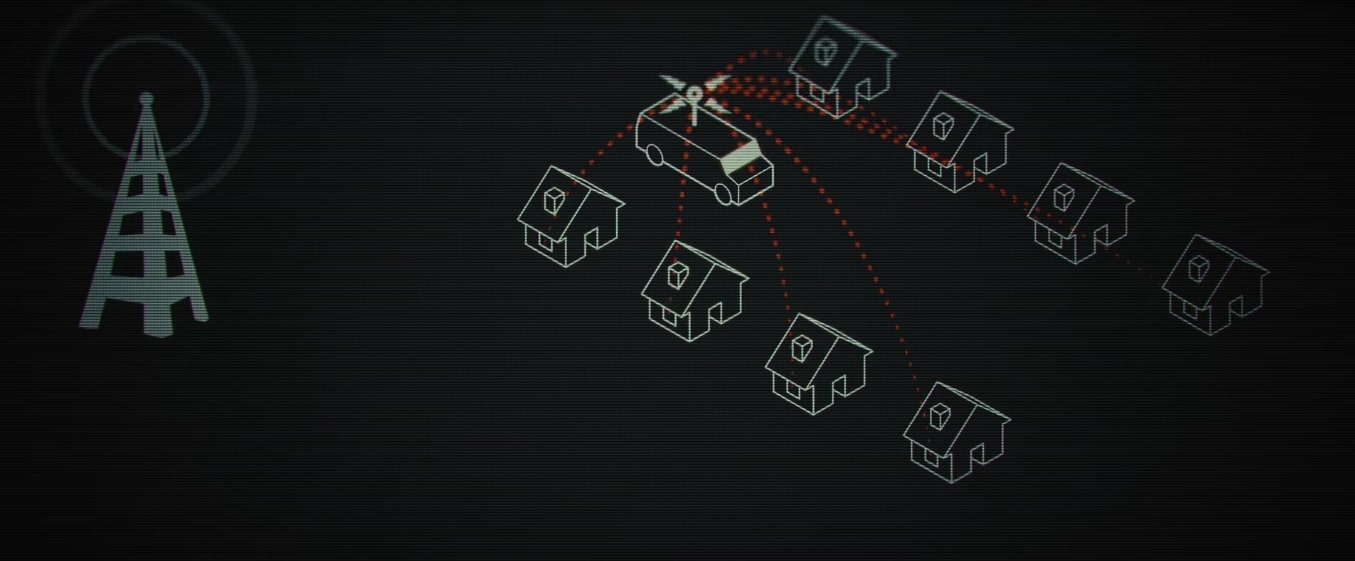
The problem with such a device is that its target is not specific — when in use to locate a suspect, it also gathers information about the phones of countless other citizens who just happen to be in the area. After all, whether handheld, mounted inside vehicles, or attached to the underside of airplanes, helicopters, and even drones, a Stingray does have notable range. The authorities thus have to move it around their doubted regions, neighborhoods, or buildings until they get the signal they’re searching for to figure out where their mark is, all the while collecting data from innocent bystanders.
We should mention that although spy surveillance technology has been around for at least a couple of decades, the use of Stingray is different because the way we use our devices now is different. Almost everything about who we are, what we do, the people we keep in touch with, and our behavioral patterns can be figured out from our cells, so some argue that it violates our privacy. That’s because Stingrays, allowing the authorities to obtain all kinds of details from a communication device without the owner even realizing it, are employed not just by the military but domestically as well.
Which Agencies Have Stingray?
As per the American Civil Liberties Union (ACLU), while at least 75 agencies in 27 states have Stingrays, this number is likely an underrepresentation since most continue to keep its use a secret. The local police in Alaska, Arizona, Georgia, Massachusetts, Missouri, Nevada, New Mexico, and Washington have these devices, whereas the state police have them in Delaware, Louisiana, New Hampshire, New Jersey, Oklahoma, and Pennsylvania.
Cell site simulators are available to both the local and the state police in California, Florida, Illinois, Indiana, Michigan, Minnesota, Maryland, New York, North Carolina, Tennessee, Texas, Virginia, and Wisconsin. As for the federal agencies known to employ the same, there is the Federal Bureau of Investigation (FBI), Internal Revenue Service (IRS), Drug Enforcement Administration (DEA), Immigration and Customs Enforcement (ICE), Bureau of Alcohol, Tobacco, Firearms, and Explosives (BATFE), and Customs and Border Protection (CBP).
Even the United States Secret Service, the Marshals Service, the Army, the Navy, the Marine Corps, the National Guard, the National Security Agency, and the United States Special Operations Command have Stingrays.
Read More: Where is Brett Johnson Now?


You must be logged in to post a comment.